How Are Public And Private Keys Generated
- How Are Public And Private Keys Generated Money
- How Are Public And Private Keys Generated 2017
- How Are Public And Private Keys Generated Florida
Finding your Private Key on Different Servers or Control Panels
Linux-Based (Apache, Nginx, LightHttpd)
Windows Operating Systems
Mac OS X
Tomcat
cPanel
WHM
Plesk
Synology NAS DSM
Webmin
VestaCP
DirectAdmin
Webuzo
Nov 15, 2017 How is a private key created for Bitcoin? With a part 2 to explain how the public key is generated. That it would take an attacker billions of years to try all the possible private keys. I'm still new to public key crypto. I'm trying to understand how it is that the private key is generated first in public key crypto? I would have expected the private and public key to be generated at the same time, as they would depend on each other. How can I find the private key for my SSL certificate. If you just got an issued SSL certificate and are having a hard time finding the corresponding private key, this article can help you to find that one and only key for your certificate. In the SSL protocol, public keys and private keys are generated by servers. The private key remains locked and secure in the server, while the public key is pinned to the server’s SSL certificate. Whenever a browser connects to the server, the server sends its SSL certificate which contains the public key. Mar 28, 2019 These keys are generated in pairs, consisting of a public key and a private key. The public key can be thought of as being an individual’s bank account, whilst the private key is the secret PIN to that bank account. The public key is cryptographically connected to a cryptocurrency address in the sense that the address is a representation of.
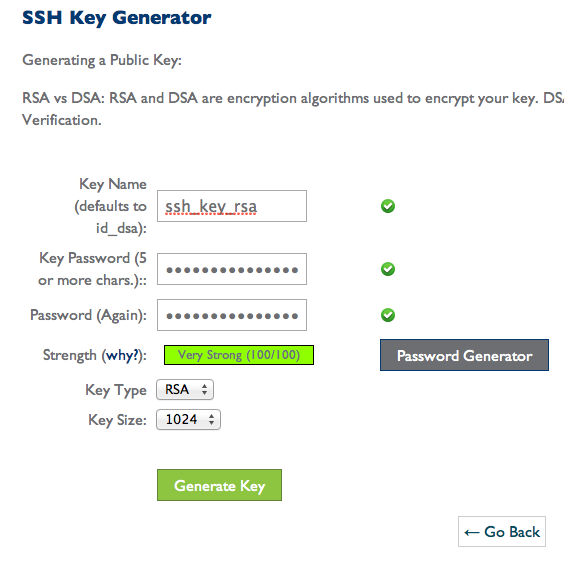
Generate online private and public key for ssh, putty, github, bitbucket. Save both of keys on your computer (text file, dropbox, evernote etc)! The generated keys are random/unique and we can't restore a missing key. You will need to copy/set the public key on to the remote server/service. How to Generate SSH Public/Private Keys on Windows. By Alexandru Andrei – Posted on Sep 17, 2019 Sep 17, 2019 in Windows. If you ever managed a Linux server from Windows, you probably used PuTTY or at least heard about it. It’s an excellent utility and has been a favorite SSH client for years.
What Is a Private Key?
What Is a Private Key?
You’ve received your SSL Certificate, and now you need to install it.
Firstly, let’s go through some basics. Public Key Infrastructure (PKI) security is about using two unique keys: the Public Key is encrypted within your SSL Certificate, while the Private Key is generated on your server and kept secret.
All the information sent from a browser to a website server is encrypted with the Public Key, and gets decrypted on the server side with the Private Key. Together the key pair keeps communication secured, and one key will not work without the other.
How do I get it?
The Private Key is generated with your Certificate Signing Request (CSR). The CSR is submitted to the Certificate Authority right after you activate your Certificate. The Private Key must be kept safe and secret on your server or device, because later you’ll need it for Certificate installation.
Note: all Certificates except Multi-Domains support Private Key generation in your browser. The key is always saved during SSL activation, we never receive this information. That’s why it’s important you save and back it up during the process if you use the in-browser automatic generation method. If the Private Key key file is lost, you’ll need to reissue your Certificate.
How Are Public And Private Keys Generated Money
Can I generate a new Private Key for my Certificate if I lose the old one?
Yes. You can generate a new private key and CSR, or use the automatic CSR and key generation during Certificate reissue (this option is available for all Certificates except for the Multi-Domains).
What does the Private Key look like?
It looks like a block of encoded data, starting and ending with headers, such as —–BEGIN RSA PRIVATE KEY—– and —–END RSA PRIVATE KEY—–.
You may not get to see this code when generating your CSR. Usually, it gets generated in the background with the CSR, and is automatically saved on your server. The system also fills the corresponding field automatically during installation of your Certificate in some control panels, such as cPanel.
The way this works varies depending on your web server, control panel, or any other tools used for CSR generation. Select the one that applies to you in the following section for specific guidance.
Finding your Private Key on Different Servers or Control Panels
Linux-based (Apache, NGINX, LightHttpd)
Normally, the CSR/RSA Private Key pairs on Linux-based operating systems are generated using the OpenSSL cryptographic engine, and saved as files with “.key” or “.pem” extensions on the server. Wow ethereum prison key.
But no specific extensions are mandatory for text files in Linux, so the key file may have any name and extension, or no extension at all.
If you remember the whole name of the key file or at least part of it, you can use the following command in your console to find the file and its directory:
The slash symbol in this command implies that the search begins from the root directory of the server. This way you have more file options to view. The name of the file in between the single quotation marks should be the part of the name that you remember. To search for the file by extension, enter “*.key” to view all the files with the “.key” extension on your server.
Tip: often the name of the file corresponds to the domain name it was generated for e.g. “domain_tld.key” or “domain.tld.pem”.
Here’s another useful command that lets you search files by their content:
This command will return the absolute path to the Private Key file if it’s located on your server.
Windows Operating Systems (IIS, Exchange, Small Business server)
Windows servers don’t let you view the Private Key in plain text format. When you import your Certificate via MMC or IIS, the Private Key is bound to it automatically if the CSR/Key pair has been generated on the same server.
If you need to obtain the Private Key to install your Certificate on a different server, you can export the key in a password protected PFX (PKCS#12) file. To do that, open the MMC Certificates snap-in tools following these steps:
Win+R >> mmc.exe >> OK >> File >> Add/Remove Snap-in >> Certificates >> Add >> Computer account >> Next >> Local computer >> Finish >> OK
Next, go to Certificate Enrollment Requests >> Certificates (if you haven’t completed the Certificate request yet). If you’ve done that, you’d select Personal >> Certificates, then right-click the Certificate >> select All Tasks >> Export. The Export wizard will open, and give you instructions. You can find more detailed instructions here.
Once that’s done, you will see the .pfx file containing your Certificate, CA-Bundle, and Private Key. To extract the key, use this tool. Choose the PKCS12 to PEM option, then upload the file and enter your chosen password.
Mac OS X
The Keychain tool in the Server application of Mac OS X won’t allow you to access the Private Key via the graphic user interface. Instead use the Terminal, by opening /etc/certificates/ directory and clicking the file.
Its name should be something like “*.key.pem”. And the terminal commands to open the file are: cd /etc/certificates/ , then ls , and sudo nano test.key.pem.
Note: to check if the Private Key matches your Certificate, go here. Then paste the Certificate and the Private Key text codes into the required fields and click Match.
Tomcat
If your Tomcat SSL connector is configured in JSSE style, the Private Key must be in a password-protected keystore file with a .jks or .keystore extension. This file, unlike most other cases, is created before the CSR. To extract the Private Key, you’ll need to convert the keystore into a PFX file with the following command:
Tips:
- “Keystore.jks” should be replaced with your actual keystore name,
- “keystore.p12” will be the name of the PKCS12 file you will receive,
- <jkskeyalias>, <jkspassword> and <keypassword> are the alias (key and keystore passwords that were entered during keystore generation),
- <jkskeyalias>, <jkspassword> and <keypassword> should be replaced with your JKS file alias, its password, and Private Key password.
- <newp12password> and <newkeypassword> should be replaced with the passwords you set for your new PKCS12 file and the Private Key.
After the PKCS12 file is generated, you can convert it to a PEM file with separated CRT, CA-Bundle and KEY files using this tool. Alternatively, use the following command in the terminal:
“Private.key” can be replaced with any key file title you like.
cPanel
- SSL/TLS Manager
a) The simplest way to get the appropriate key used during SSL installation is reflected in the below picture:
b) Alternatively, you can find the Private key in the Private keys section of the SSL/TLS Manager, which can be located in the cPanel main menu. You will see all the Private Keys ever generated in your cPanel. To view the code of the key, click View & Edit. If there are several keys in that menu, you can copy each of them to find a match with your Certificate code by using this tool. - File manager
On the homepage of your cPanel, click File manager. Find the folder named “ssl” in the folder tree to the left (see screenshot). That folder will contain another folder named “keys”. This key folder also contains all the keys ever generated in your cPanel.
WHM
WHM stores your private keys and CSR codes in the SSL Storage Manager menu. On the homepage, click SSL/TLS >> SSL Storage Manager. To view the Private Key, click the magnifier icon next to the relevant key in the Key column.
Plesk
Click Domains >> your domain >> SSL/TLS Certificates. You’ll see a page like the one shown below. The key icon with the message “Private key part supplied” means there is a matching key on your server.
To get it in plain text format, click the name and scroll down the page until you see the key code. Alternatively, click the green arrow icon on the right. This will download a PEM file, containing your Private Key, Certificate and CA-Bundle files (if they were previously imported to the server). The files can be opened in any text editor, such as Notepad.
Synology NAS DSM
When generating a CSR in Synology DSM, the Private Key is provided to you in a zip file on the last step. The key code is contained within a server.key file, that can be opened with a text editor, such as Notepad.
Webmin
Webmin works as a graphic user interface (GUI) on top of the command-line interface. There is also a file manager called Filemin, that you can use to browse the server file system and find your Private Key file. Alternatively, go to Others >> Command Shell and run the find or grep command, which you can find in the Linux Operating Systems section above.
VestaCP
Your Private Key needs to be saved during CSR generation, as it will not be available via the graphic user interface.
That said, you may be able to retrieve your Private Key via SSH. It is saved as a temporary file in the “/tmp” folder. The path to the file will look something like this: “/tmp/tmp.npAnkmWFcu/domain.com.key”.
Note: the files in the /tmp directory are deleted every time your server is rebooted, so this is not a safe place to store your Private Key.
To get the path to your key file, use this Linux command:
Where you see “domain.com”, replace this with the actual domain name you generated the CSR for.
The path to your key file can also be found using the grep command:
DirectAdmin
In the up-to-date version of DirectAdmin, your Private Key is saved on the server. Access it in the “Paste a pre-generated Certificate and key” field during installation.
Simcity 5 beta download. Our SimCity 5 Keygen generates serial key for SimCity 5. You can unlock full game and play for free by using our keygen and crack for free. This Crack & Keygen is tested on daily basis under the guidance of experts and it is working perfectly. This Crack & KeyGen is Newest and Working perfectly. May 26, 2019 Simcity 5 Serial key generator: Simcity 5 Keygen will generate the secured and safe keys for the full game version to let the game lovers enjoy this fantastic game for free. The keys are totally secured and virus-free, and you just need them to activate the game version.
If that section is empty, it may mean the CSR and key were generated elsewhere, or the key was not saved in DirectAdmin due to a glitch. If a glitch happened, try retrieving the key via SSH. Usually it is saved in this directory:
/usr/local/directadmin/data/users/<user>/domains/<domain>.key
Note: <user> and <domain> are your DirectAdmin details.
How Are Public And Private Keys Generated 2017
Webuzo
On the homepage, find the SSL management section by clicking the Private Keys button. This will display a list of all the Private Keys generated in Webuzo. To see the key code, click the pencil icon to the right under the Option column, as shown in the screenshot below:
To sum up, ways to find your private key fully depend on the interface of the web server where you generate the CSR. If the methods described above did not help you find the private key for your certificate, the only solution would be to generate a new CSR/private key pair and reissue your certificate and to make sure that the key is saved on your server/local computer this time.
Key generation is the process of generating keys in cryptography. A key is used to encrypt and decrypt whatever data is being encrypted/decrypted.
A device or program used to generate keys is called a key generator or keygen.
Generation in cryptography[edit]
Modern cryptographic systems include symmetric-key algorithms (such as DES and AES) and public-key algorithms (such as RSA). Symmetric-key algorithms use a single shared key; keeping data secret requires keeping this key secret. Public-key algorithms use a public key and a private key. The public key is made available to anyone (often by means of a digital certificate). A sender encrypts data with the receiver's public key; only the holder of the private key can decrypt this data.
Since public-key algorithms tend to be much slower than symmetric-key algorithms, modern systems such as TLS and SSH use a combination of the two: one party receives the other's public key, and encrypts a small piece of data (either a symmetric key or some data used to generate it). The remainder of the conversation uses a (typically faster) symmetric-key algorithm for encryption.
Computer cryptography uses integers for keys. In some cases keys are randomly generated using a random number generator (RNG) or pseudorandom number generator (PRNG). A PRNG is a computeralgorithm that produces data that appears random under analysis. PRNGs that use system entropy to seed data generally produce better results, since this makes the initial conditions of the PRNG much more difficult for an attacker to guess. Another way to generate randomness is to utilize information outside the system. veracrypt (a disk encryption software) utilizes user mouse movements to generate unique seeds, in which users are encouraged to move their mouse sporadically. In other situations, the key is derived deterministically using a passphrase and a key derivation function.
Many modern protocols are designed to have forward secrecy, which requires generating a fresh new shared key for each session.
Classic cryptosystems invariably generate two identical keys at one end of the communication link and somehow transport one of the keys to the other end of the link.However, it simplifies key management to use Diffie–Hellman key exchange instead.
The simplest method to read encrypted data without actually decrypting it is a brute-force attack—simply attempting every number, up to the maximum length of the key. Therefore, it is important to use a sufficiently long key length; longer keys take exponentially longer to attack, rendering a brute-force attack impractical. Currently, key lengths of 128 bits (for symmetric key algorithms) and 2048 bits (for public-key algorithms) are common.
Generation in physical layer[edit]
Wireless channels[edit]
A wireless channel is characterized by its two end users. By transmitting pilot signals, these two users can estimate the channel between them and use the channel information to generate a key which is secret only to them.[1] The common secret key for a group of users can be generated based on the channel of each pair of users.[2]
How Are Public And Private Keys Generated Florida
Optical fiber[edit]
A key can also be generated by exploiting the phase fluctuation in a fiber link.[clarification needed]
See also[edit]
- Distributed key generation: For some protocols, no party should be in the sole possession of the secret key. Rather, during distributed key generation, every party obtains a share of the key. A threshold of the participating parties need to cooperate to achieve a cryptographic task, such as decrypting a message.
References[edit]
- ^Chan Dai Truyen Thai; Jemin Lee; Tony Q. S. Quek (Feb 2016). 'Physical-Layer Secret Key Generation with Colluding Untrusted Relays'. IEEE Transactions on Wireless Communications. 15 (2): 1517–1530. doi:10.1109/TWC.2015.2491935.
- ^Chan Dai Truyen Thai; Jemin Lee; Tony Q. S. Quek (Dec 2015). 'Secret Group Key Generation in Physical Layer for Mesh Topology'. 2015 IEEE Global Communications Conference (GLOBECOM). San Diego. pp. 1–6. doi:10.1109/GLOCOM.2015.7417477.