Git Generate Public Ssh Key
- Generate Public Ssh Key
- Generate Public Ssh Key For Git
- Git Generate Public Ssh Key Mac
- Create Ssh Key Git
- Git Generate Public Ssh Key From Private Ssh Key
Azure Repos Azure DevOps Server 2019 TFS 2018 TFS 2017 TFS 2015 Update 3
Connect to your Git repos through SSH on macOS, Linux, or Windows to securely connect using HTTPS authentication. On Windows, we recommended the use of Git Credential Managers or Personal Access Tokens.
Important
SSH URLs have changed, but old SSH URLs will continue to work. If you have already set up SSH, you should update your remote URLs to the new format:
- Verify which remotes are using SSH by running
git remote -vin your Git client. - Visit your repository on the web and select the Clone button in the upper right.
- Select SSH and copy the new SSH URL.
- In your Git client, run:
git remote set-url <remote name, e.g. origin> <new SSH URL>. Alternatively, in Visual Studio, go to Repository Settings, and edit your remotes.
Sep 26, 2019 To generate an SSH key with PuTTYgen, follow these steps: Open the PuTTYgen program. For Type of key to generate, select SSH-2 RSA. Click the Generate button. Move your mouse in the area below the progress bar. When the progress bar is full, PuTTYgen generates your key pair. That being said, many Git servers authenticate using SSH public keys. In order to provide a public key, each user in your system must generate one if they don’t already have one. This process is similar across all operating systems. First, you should check to make sure you don’t already have a key. By default, a user’s SSH keys are stored in that user’s /.ssh directory. You can easily check to see if you have a key. How to generate a public key(to be used in GitHub/GitLab) using command line Git Bash. The command below generates the error sh.exe': syntax error near unexpected token '(' I am using windows xp. $ ssh-keygen -t rsa -C 'xxxx@gmail.com' Generating public/private rsa key pair. Jul 25, 2019 When you create private/public SSH keys on your machine (that’s what you did in the above steps), it’s not enough. You need to give your public key to the repository in order to pair the Git server with your local machine (that’d be steps 4. We get a note that we currently do not have any public SSH keys in our GitHub account and followed by the links to generate one. So, our learning in the SSH authentication post is quite right. We need the keys to communicate with the server via SSH. In the next section, we will generate the SSH keys, but before that, as a precaution, you should remember a note.
Note
As of Visual Studio 2017, SSH can be used to connect to Git repos.
How SSH key authentication works
SSH public key authentication works with an asymmetric pair of generated encryption keys. The public key is shared with Azure DevOps and used to verify the initial ssh connection. The private key is kept safe and secure on your system.
Set up SSH key authentication
The following steps cover configuration of SSH key authentication on the following platforms:

- Linux
- macOS running at least Leopard (10.5)
- Windows systems running Git for Windows
Configure SSH using the command line. bash is the common shell on Linux and macOS and the Git for Windows installation adds a shortcut to Git Bash in the Start menu.Other shell environments will work, but are not covered in this article.
Step 1: Create your SSH keys
Note
If you have already created SSH keys on your system, skip this step and go to configuring SSH keys.
The commands here will let you create new default SSH keys, overwriting existing default keys. Before continuing, check your~/.ssh folder (for example, /home/jamal/.ssh or C:Usersjamal.ssh) and look for the following files:
- id_rsa
- id_rsa.pub
If these files exist, then you have already created SSH keys. You can overwrite the keys with the following commands, or skip this step and go to configuring SSH keys to reuse these keys.
Create your SSH keys with the ssh-keygen command from the bash prompt. This command will create a 2048-bit RSA key for use with SSH. You can give a passphrasefor your private key when prompted—this passphrase provides another layer of security for your private key.If you give a passphrase, be sure to configure the SSH agent to cache your passphrase so you don't have to enter it every time you connect.
This command produces the two keys needed for SSH authentication: your private key ( id_rsa ) and the public key ( id_rsa.pub ). It is important to never share the contents of your private key. If the private key iscompromised, attackers can use it to trick servers into thinking the connection is coming from you.
Step 2: Add the public key to Azure DevOps Services/TFS
Associate the public key generated in the previous step with your user ID.
Open your security settings by browsing to the web portal and selecting your avatar in the upper right of theuser interface. Select Security in the menu that appears.
Select SSH public keys, and then select + New Key.
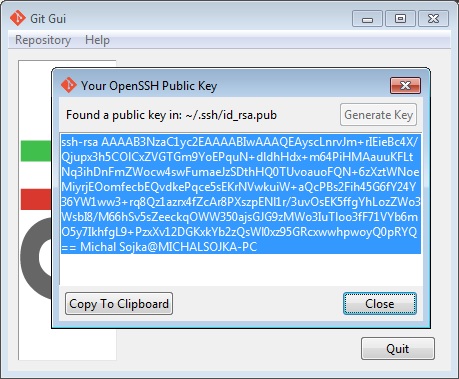
Copy the contents of the public key (for example, id_rsa.pub) that you generated into the Public Key Data field.
Important
Avoid adding whitespace or new lines into the Key Data field, as they can cause Azure DevOps Services to use an invalid public key. When pasting in the key, a newline often is added at the end. Be sure to remove this newline if it occurs.
Give the key a useful description (this description will be displayed on the SSH public keys page for your profile) so that you can remember it later. Select Save to store the public key. Once saved, you cannot change the key. You can delete the key or create a new entry for another key. There are no restrictions on how many keys you can add to your user profile.
Generate Public Ssh Key
Step 3: Clone the Git repository with SSH
Note
To connect with SSH from an existing cloned repo, see updating your remotes to SSH.
Copy the SSH clone URL from the web portal. In this example, the SSL clone URL is for a repo in an organization named fabrikam-fiber, as indicated by the first part of the URL after
dev.azure.com.Note
Project URLs have changed with the release of Azure DevOps Services and now have the format
dev.azure.com/{your organization}/{your project}, but you can still use the existingvisualstudio.comformat. For more information, see VSTS is now Azure DevOps Services.Run
git clonefrom the command prompt.
SSH may display the server's SSH fingerprint and ask you to verify it.
For cloud-hosted Azure DevOps Services, where clone URLs contain either ssh.dev.azure.com or vs-ssh.visualstudio.com, the fingerprint should match one of the following formats:
- MD5:
97:70:33:82:fd:29:3a:73:39:af:6a:07:ad:f8:80:49(RSA) - SHA256:
SHA256:ohD8VZEXGWo6Ez8GSEJQ9WpafgLFsOfLOtGGQCQo6Og(RSA)These fingerprints are also listed in the SSH public keys page.
For self-hosted instances of Azure DevOps Server, you should verify that the displayed fingerprint matches one of the fingerprints in the SSH public keys page.
SSH displays this fingerprint when it connects to an unknown host to protect you from man-in-the-middle attacks.Once you accept the host's fingerprint, SSH will not prompt you again unless the fingerprint changes.
When you are asked if you want to continue connecting, type yes. Git will clone the repo and set up the origin remote to connect with SSH for future Git commands.
Tip
Avoid trouble: Windows users will need to run a command to have Git reuse their SSH key passphrase.
Questions and troubleshooting
Q: After running git clone, I get the following error. What should I do?
Host key verification failed.fatal: Could not read from remote repository.
A: Manually record the SSH key by running:ssh-keyscan -t rsa domain.com >> ~/.ssh/known_hosts
Q: How can I have Git remember the passphrase for my key on Windows?
A: Run the following command included in Git for Windows to start up the ssh-agent process in Powershell or the Windows Command Prompt. ssh-agent will cacheyour passphrase so you don't have to provide it every time you connect to your repo.
If you're using the Bash shell (including Git Bash), start ssh-agent with:
Q: I use PuTTY as my SSH client and generated my keys with PuTTYgen. Can I use these keys with Azure DevOps Services?
A: Yes. Load the private key with PuTTYgen, go to Conversions menu and select Export OpenSSH key.Save the private key file and then follow the steps to set up non-default keys.Copy your public key directly from the PuTTYgen window and paste into the Key Data field in your security settings.
Q: How can I verify that the public key I uploaded is the same key as I have locally?
A: You can verify the fingerprint of the public key uploaded with the one displayed in your profile through the following ssh-keygen command run against your public key usingthe bash command line. You will need to change the path and the public key filename if you are not using the defaults.
You can then compare the MD5 signature to the one in your profile. This check is useful if you have connection problems or have concerns about incorrectlypasting in the public key into the Key Data field when adding the key to Azure DevOps Services.
Q: How can I start using SSH in a repository where I am currently using HTTPS?
A: You'll need to update the origin remote in Git to change over from a HTTPS to SSH URL. Once you have the SSH clone URL, run the following command:
You can now run any Git command that connects to origin.
Q: I'm using Git LFS with Azure DevOps Services and I get errors when pulling files tracked by Git LFS.
A: Azure DevOps Services currently doesn't support LFS over SSH. Use HTTPS to connect to repos with Git LFS tracked files.
Q: How can I use a non default key location, i.e. not ~/.ssh/id_rsa and ~/.ssh/id_rsa.pub?
A: To use keys created with ssh-keygen in a different place than the default, you do two things:
- The keys must be in a folder that only you can read or edit. If the folder has wider permissions, SSH will not use the keys.
- You must let SSH know the location of the keys. You make SSH aware of keys through the
ssh-addcommand, providing the full path to the private key.
On Windows, before running ssh-add, you will need to run the following command from included in Git for Windows:
This command runs in both Powershell and the Command Prompt. If you are using Git Bash, the command you need to use is:
You can find ssh-add as part of the Git for Windows distribution and also run it in any shell environment on Windows.
On macOS and Linux you also must have ssh-agent running before running ssh-add, but the command environment on these platforms usuallytakes care of starting ssh-agent for you.
Q: I have multiple SSH keys. How do I use different SSH keys for different SSH servers or repos?
A: Generally, if you configure multiple keys for an SSH client and connect to an SSH server, the client can try the keys one at a time until the server accepts one.
However, this doesn't work with Azure DevOps for technical reasons related to the SSH protocol and how our Git SSH URLs are structured. Azure DevOps will blindly accept the first key that the client provides during authentication. If that key is invalid for the requested repo, the request will fail with the following error:
 Vue - how to create unique key with v-for=“item in 3”. Browse other questions tagged vue.js key or ask your own question. The Overflow Blog You like our dark mode? Well, wait until you try our Ultra Dark Mode. Podcast 223: Embrace the Darkness. Featured on Meta. To Nihat's point (above): Evan You has advised against using uid: 'The vm uid is reserved for internal use and it's important to keep it private (and not rely on it in user code) so that we keep the flexibility to change its behavior for potential future use cases. Jul 27, 2017 Vue won't generate unique keys for you, there is no point in this. The developer needs to provide unique keys because Vue can't guess them. Also, Vue mutating your objects on its own would be very wrong in my opinion. If your data don't have any field that could be used as unique keys, there is something not right about it, ask your backend team. Mar 28, 2012 I had an issue that I'm using a v-for in Vue.js on a component, but in Vue 2.2+ you required:key to be set with a unique identifier. In my case the Array that it iterates over doesn't have any, so I had to generate one on demand (imagine a Bootstrap alerts manager component, e.g.). This will do just fine.
Vue - how to create unique key with v-for=“item in 3”. Browse other questions tagged vue.js key or ask your own question. The Overflow Blog You like our dark mode? Well, wait until you try our Ultra Dark Mode. Podcast 223: Embrace the Darkness. Featured on Meta. To Nihat's point (above): Evan You has advised against using uid: 'The vm uid is reserved for internal use and it's important to keep it private (and not rely on it in user code) so that we keep the flexibility to change its behavior for potential future use cases. Jul 27, 2017 Vue won't generate unique keys for you, there is no point in this. The developer needs to provide unique keys because Vue can't guess them. Also, Vue mutating your objects on its own would be very wrong in my opinion. If your data don't have any field that could be used as unique keys, there is something not right about it, ask your backend team. Mar 28, 2012 I had an issue that I'm using a v-for in Vue.js on a component, but in Vue 2.2+ you required:key to be set with a unique identifier. In my case the Array that it iterates over doesn't have any, so I had to generate one on demand (imagine a Bootstrap alerts manager component, e.g.). This will do just fine.
Generate Public Ssh Key For Git
For Azure DevOps, you'll need to configure SSH to explicitly use a specific key file. One way to do this to edit your ~/.ssh/config file (for example, /home/jamal/.ssh or C:Usersjamal.ssh) as follows:
Q: What notifications may I receive about my SSH keys?
A: Whenever you register a new SSH Key with Azure DevOps Services, you will receive an email notification informing you that a new SSH key has been added to your account.
Q: What do I do if I believe that someone other than me is adding SSH keys on my account?
A: If you receive a notification of an SSH key being registered and you did not manually upload it to the service, your credentials may have been compromised.
The next step would be to investigate whether or not your password has been compromised. Changing your password is always a good first step to defend against this attack vector. If you’re an Azure Active Directory user, talk with your administrator to check if your account was used from an unknown source/location.
Objectives
- Explain what an SSH key is
- Generate your own SSH key pair
- Add your SSH key to your GitHub account
- Learn how to use your SSH key in your GitHub workflow
Why Use an SSH Key?
When working with a GitHub repository, you'll often need to identify yourself to GitHub using your username and password. An SSH key is an alternate way to identify yourself that doesn't require you to enter you username and password every time.
SSH keys come in pairs, a public key that gets shared with services like GitHub, and a private key that is stored only on your computer. If the keys match, you're granted access.
The cryptography behind SSH keys ensures that no one can reverse engineer your private key from the public one.
Generating an SSH key pair
The first step in using SSH authorization with GitHub is to generate your own key pair.
You might already have an SSH key pair on your machine. You can check to see if one exists by moving to your .ssh directory and listing the contents.
If you see id_rsa.pub, you already have a key pair and don't need to create a new one.
If you don't see id_rsa.pub, use the following command to generate a new key pair. Make sure to replace your@email.com with your own email address.
(The -o option was added in 2014; if this command fails for you, just remove the -o and try again)
When asked where to save the new key, hit enter to accept the default location.
You will then be asked to provide an optional passphrase. This can be used to make your key even more secure, but for this lesson you can skip it by hitting enter twice.
When the key generation is complete, you should see the following confirmation:
The random art image is an alternate way to match keys but we won't be needing this.
Add your public key to GitHub
We now need to tell GitHub about your public key. Display the contents of your new public key file with cat:
The output should look something like this:
Copy the contents of the output to your clipboard.
Login to github.com and bring up your account settings by clicking the tools icon.
Select SSH Keys from the side menu, then click the Add SSH key button.
Name your key something whatever you like, and paste the contents of your clipboard into the Key text box.
Git Generate Public Ssh Key Mac
Finally, hit Add key to save. Enter your github password if prompted.
Create Ssh Key Git
####Using Your SSH Key
Going forward, you can use the SSH clone URL when copying a repo to your local machine.
This will allow you to bypass entering your username and password for future GitHub commands.
Git Generate Public Ssh Key From Private Ssh Key
Key Points
- SSH is a secure alternative to username/password authorization
- SSH keys are generated in public / private pairs. Your public key can be shared with others. The private keys stays on your machine only.
- You can authorize with GitHub through SSH by sharing your public key with GitHub.